过抓包
万事开始先说抓包,说起抓包根据前辈们的信息能找到很多,我这里总结一手
tiktok加密参数分析_tiktik iid-CSDN博客
先说boringssl,这个东西就是是 Google 为 Android 等项目定制的轻量级、精简版的 OpenSSL,用于实现加密通信和安全协议。SSL_CTX_set_custom_verify 是 BoringSSL 中用于设置自定义证书验证逻辑的函数。它的函数原型大致如下:void SSL_CTX_set_custom_verify(SSL_CTX *ctx, int mode, ssl_custom_verify_callback callback);参数解释:
- ctx:要设置的 SSL 上下文(SSL_CTX)。
- mode:验证模式(比如 SSL_VERIFY_PEER)。
- callback:你自己实现的回调函数,用于处理证书验证逻辑。
直接让上面那个函数返回0即可
logger("[*][*] Waiting for libttboringssl...");
waitForModule("libttboringssl.so").then((lib) => {
logger(`[*][+] Found libttboringssl at: ${lib.base}`)
hook_SSL_CTX_set_custom_verify(lib);
});
function logger(message) {
console.log(message);
Java.perform(function() {
var Log = Java.use("android.util.Log");
Log.v("TIKTOK_SSL_PINNING_BYPASS", message);
});
}
function hook_callback(callback) {
const f = new NativeFunction(callback, "int", ["pointer", "pointer"]);
Interceptor.attach(f, {
onLeave: function(retval) {
retval.replace(0)
}
})
}
function waitForModule(moduleName) {
return new Promise(resolve => {
const interval = setInterval(() => {
const module = Process.findModuleByName(moduleName);
if (module != null) {
clearInterval(interval);
resolve(module);
}
}, 0);
});
}
function hook_SSL_CTX_set_custom_verify(library) {
const functionName = "SSL_CTX_set_custom_verify"
try {
const f = Module.getExportByName(library.name, functionName);
const SSL_CTX_set_custom_verify = new NativeFunction(f, 'void', ['pointer', 'int', 'pointer'])
Interceptor.replace(SSL_CTX_set_custom_verify, new NativeCallback(function(ssl, mode, callback) {
hook_callback(callback);
SSL_CTX_set_custom_verify(ssl, mode, callback)
}, 'void', ['pointer', 'int', 'pointer']));
logger(`[*][+] Hooked function: ${functionName}`);
} catch (err) {
logger(`[*][-] Failed to hook function: ${functionName}`);
logger(err.toString())
}
}接下来就是老生常谈的加密参数了
TikTok使用cronet网络库。将libsscronet拖IDA反编译
然后可以发现一些关键词可以看见关键代码,然后定位到这里,丢给ai分析,发现这里像是拼接的函数
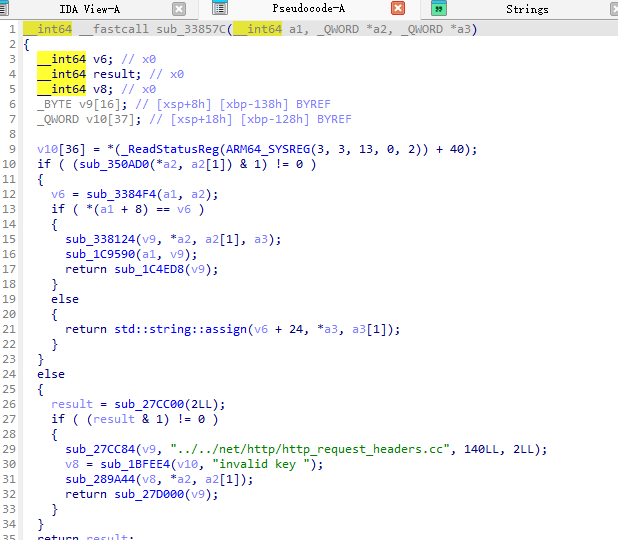
hook一手顺便查一下调用
Interceptor.attach(lib.add(0x33857C), {
onEnter: function (args) {
var key = args[1].readPointer().readUtf8String();
var val = args[2].readPointer().readUtf8String();
console.log(key + " : " + val);
if (key.indexOf("X-Gorgon") !== -1) {
console.log('SetHeaders called from:\n' + Thread.backtrace(this.context, Backtracer.ACCURATE).map(DebugSymbol.fromAddress).join('\n') + '\n');
console.log("---------------------------end----------------------------------");
}
},
onLeave: function (retval) {
}
});发现这个很像
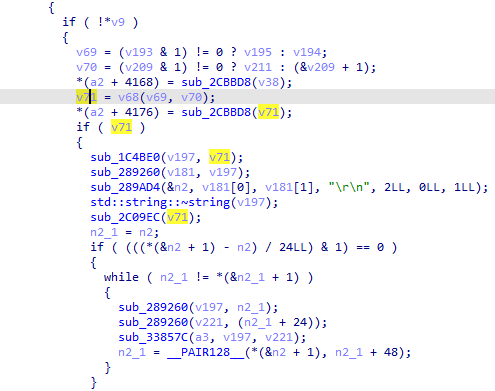
v71是从另一个so中调取
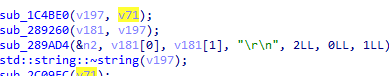
这里是一些分割,所以hook这个跳转,可以得到加密传入参数和结果
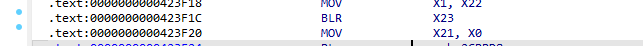
Interceptor.attach(lib.add(0x423F1C), {
onEnter: function (args) {
let result = args[0].readUtf8String();
//console.log('===================start==========================');
if(result.indexOf("v1/message/send") != -1)
{
console.log('SetHeaders called from:\n' + Thread.backtrace(this.context, Backtracer.ACCURATE).map(DebugSymbol.fromAddress).join('\n') + '\n');
console.log(args[0].readUtf8String());
console.log('=============================================');
console.log(args[1].readUtf8String());
console.log('=============================================');
console.log("X23_offset:" + this.context.x23);
console.log('===================end==========================');
}
},
onLeave: function (retval) {
}
});